Storing, processing, and gaining insights from data is a necessity for companies to deliver innovative services in almost every industry. When some of this data includes sensitive information, such as personal details, we (the people, or “data subjects” whose personal details are stored) expect it to be stored securely, so it will not be exposed unnecessarily.
Over the years, there have been so many data breaches that sometimes it feels like we, as data subjects, almost expect the data we submit online to find its way to attackers or the public. However, we should not accept this norm. In response, regulators and companies have spent significant time, money, and energy to ensure that data is secure, especially personal information.
We surveyed industry experts to get a snapshot of the data security landscape. The results from this survey are presented in the State of DataSecOps Report 2022. This report describes how organizations handle their data security and employee access to data, and achieve data innovation despite having to ensure this sensitive data remains private, secure, and well-governed.
We present some of the questions that were asked during the survey and a summary of the responses.
To read more:
The Full Report
Some of the Questions Answered By The Survey
The respondents included nearly 300 data engineers, architects, and scientists, as well as security, privacy, and compliance professionals from over 100 hyper-growth startups, and mid-size and Fortune 500 companies.
Do organizations store sensitive financial data in data stores?
Almost half of all 42% of respondents indicated that they maintain sensitive financial data such as credit scores, bank or credit card accounts, and payments in their data stores.
Do organizations store PII (Personal Identifiable Information) in data stores?
A significant portion of the organizations included in the survey, 74%, save sensitive PII (personal identifiable data), such as names, email addresses, and phone numbers in their data stores.
Where is sensitive data stored in companies?
According to the survey, those organizations that have sensitive data (data containing personal, health, or financial data) store at least 10% of it within their data repositories.
What business function is responsible for securing access to sensitive data?
Respondents equally identified (35%) security teams and data services teams (data engineering and architecture) as responsible for securing sensitive data responses. This was followed by compliance or privacy teams at 20%, while 10% of the respondents believe that security is the responsibility of the data science or analytics teams (the data consumers or producers).
Is data access increasing or decreasing in the industry?
Data access is becoming increasingly important, three quarters of the respondents answered that they are working on projects enabling consumers to gain more access to data.
How do companies know where sensitive data is?
Ideally, companies should have fresh metadata, especially regarding the location of sensitive data. However, only 28% of the respondents have a process in place that continuously discovers sensitive data.
How frequently do companies scan for sensitive data?
According to the respondents approximately half (44%) of the organizations that monitor sensitive data periodically only do so quarterly or annually.
What are the top data security concerns for companies?
An overwhelming 85% of respondents, ranked exposure of customer data as a top data security concern. Additional, main concerns included:
- Meeting customer requirements for data security, privacy, or compliance (70%)
- Complying with consumer privacy regulations such as GDPR or CCPA (69%)
How is data access managed in organizations?
Data access requests are primarily handled manually; with 61% of respondents from the companies surveyed relying on manual processes and tools to manage data access requests. In contrast, only one out of five indicated that they have fully automated processes.
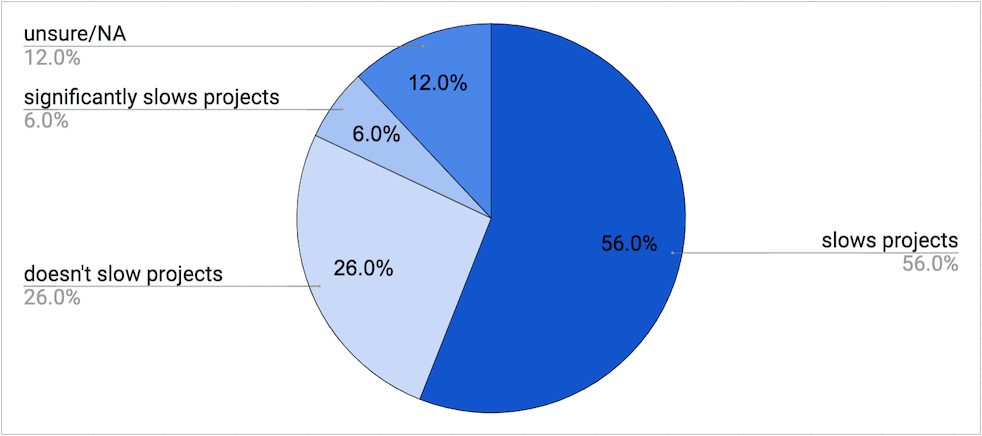
Do security & compliance requirements slow down data projects?
While incredibly important, security and compliance requirements do slow down data projects according to over 50% of the respondents.
Do data engineers like to work on security and compliance projects?
A majority, more than 50%, of respondents would rather spend less time working on security and compliance requirements. Instead, they would prefer to focus their attention on core engineering projects.
Learning from the results
We conducted this survey to gain a better understanding of the overall data security outlook. In particular, we focused on:
- The type and the extent of sensitive customer data contained in the data infrastructure and current processes and tools used to find and classify the data.
- Identify who is responsible for securing access to sensitive data and what processes and tools are used for implementing security measures.
- Benchmark the effort required to meet data security, governance, and compliance requirements and determine areas of improvement for processes and tools.
Summary of the Findings
The main takeaways from the report:
1. It’s all about the sensitive data
Respondents are wary of handling sensitive data, they are particularly concerned about exposure of sensitive data, which they overwhelmingly noted was their biggest concern. Further, sensitive data is prevalent in their data stores, with over two-thirds of the respondents indicating the data within their data stores includes PII.
As concerned as they are about sensitive data, and as they continue to increase consumer access to data, many of these companies do not have processes to continuously discover sensitive data, or not in any effective way. This is a significant dichotomy for companies as they want to reduce their risk exposure while simultaneously increasing access. It is critical for companies to implement processes that provide information and continuously update the location of sensitive data.
2. We are still at the ‘expansion’ phase of “data democratization”.
Data democratization is essentially getting more value from data by providing greater access to people within the organization. The increase in access strengthens the ability of the organization to extract value from having all of this data.
The bad news: it is still not a “working reality” for many organizations.
The good news: it is a “work in progress” project for many organizations. Roughly 75% of the respondents are involved in projects aimed at making data more accessible, meaning that in the future more users in more organizations will be able to create more value from data. However, organizations must be careful to ensure that this access is controlled to meet security and risk compliance regulations as well as protect sensitive data.
3. Data operations are lagging behind the automation of security controls.
The majority of companies still rely on manual processes to authorize access to users. Data engineers, who are primarily responsible for this task, feel like this pulls them away from their core engineering projects and falls outside of their wheelhouse. This places the company in an uncomfortable position of having time-intensive processes implemented by teams who would prefer to be working on other tasks. Therefore, these organizations should consider their efforts to implement self-service data access and rely less on manual authorization.
State of DataSecOps Report 2022 - Methodology
To create the report, we surveyed 295 verified professionals in the data security space. The surveyed professionals that participated in the study were data engineers, architects, and scientists, as well as security, privacy, and compliance professionals from over 100 hyper-growth startups, and mid-size and Fortune 500 companies.
Hyper-growth startups in Fintech, Healthtech, and B2B and B2C Tech including Payfit, Sezzle, Square, Asurion, Lucid, Filevine, Innovaccer, Uniphore, Letsgetchecked, Cloudflare, Wayfair, Yelp, Trade Republic Bank, Talkdesk, 54gene, Collective Health, Tricore Technology, and Snap Inc.
Fortune 500 companies across financial services, healthcare, technology, manufacturing, retail, and e-commerce including Bank of America, JPMorgan Chase, HSBC, Credit Suisse, Vanguard, Visa, Equifax, UnitedHealth Group, Optum, IBM, Amazon, Accenture, Cisco, Google, AT&T, ViacomCBS (Paramount), T-Mobile, Lowe’s, Shopify, DHL, Kroger, and Walmart.
The survey was conducted in March and April of 2022 for Satori by Data Science Connect, a community of over 20,000 data and analytics professionals across North America.
Conclusion
In the survey, we were able to quantify ideas and comments we had heard from hundreds of data and security leaders we spoke with over the years. These are exciting times for data in general, and for companies who will be able to adopt a DataSecOps approach to streamline secure access to data.
To learn more about Satori:
Or read about: